A Guide to Absolute Digital Freedom
This is your key to the back door of the digital world, an entry point to the uncensored, unmonitored chaos of the darknet where true freedom still breathes.
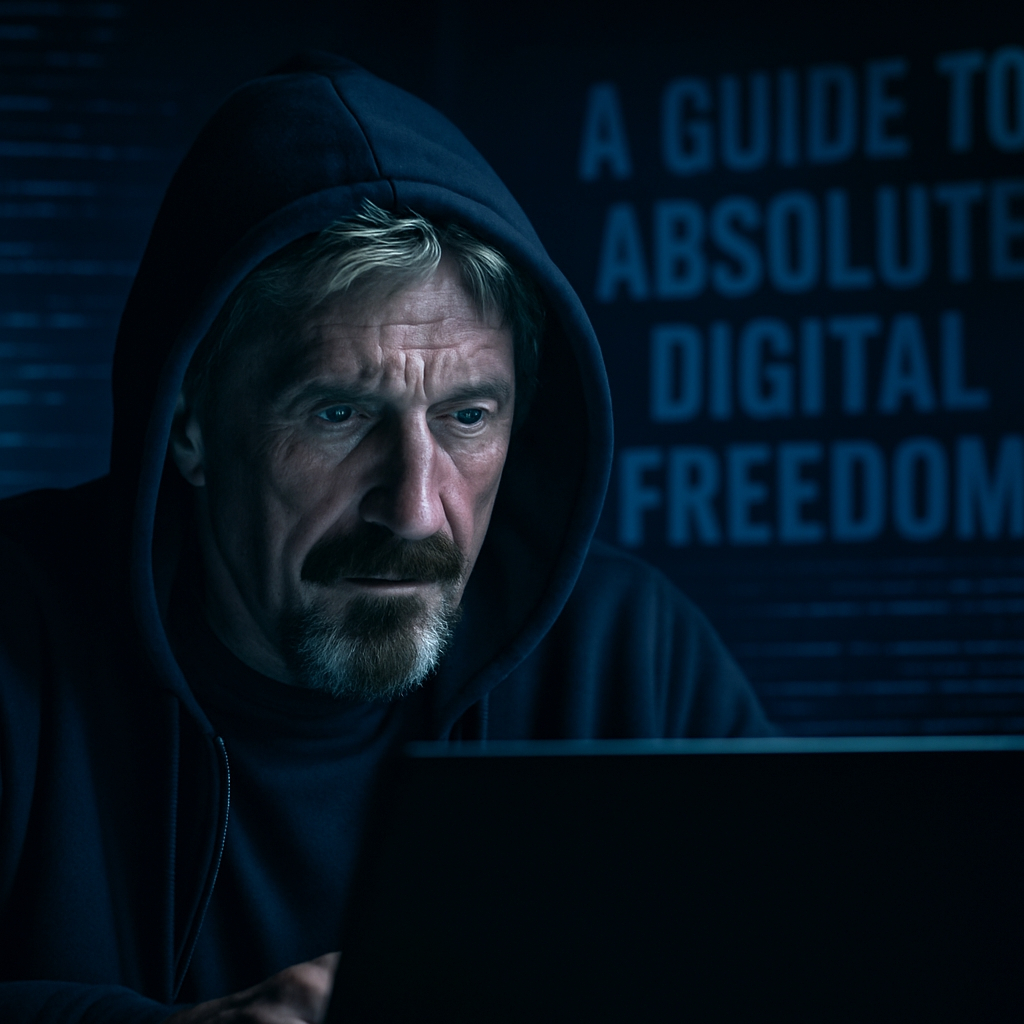
A Preamble from the Ghost in the Machine
It’s five-forty in the afternoon here in Venezuela, or wherever the hell I am this week. The sun is a molten gold bleeding into the Caribbean, the air is thick with salt and the smell of cheap gasoline, and I’m surrounded by beautiful women, armed guards, and enough satellite uplinks to wage a small war from this laptop. To the outside world, I’m a madman. A fugitive. A headline. And maybe I am. But let me tell you what else I am: I am a free man.
Can you say the same?
Look at your life. You wake up, you check your phone—a tracking device made by a trillion-dollar corporation in a communist country. You go to work, tracked by GPS in your car. You buy a coffee with a credit card, leaving a digital breadcrumb. You sit at your desk and type your thoughts into a computer running an operating system designed by a company that has a standing invitation for three-letter agencies to come in and rifle through your digital underwear drawer.
You are living in a cage with invisible bars. A panopticon. And the most beautiful, diabolical part of it all is that you helped build it. You traded your freedom for convenience. You traded your privacy for cat videos and the dopamine hit of a "like" from a stranger you'll never meet.
I’ve spent my entire goddamn life on the front lines of this war. I created the first antivirus, a shield against the digital plagues of the early internet. Then I watched as the real plague emerged: not viruses, but the insatiable hunger for data and control from governments and corporations. They are the new gods, and your personal information is their ambrosia.
This document you're reading is not a "how-to" guide. It is a declaration of war. It is an escape plan. It is the collected wisdom of a man who has lived for decades with the hounds of hell nipping at his heels and has never once been collared. I have been hunted by the most powerful entities on this planet, and I am still here, sipping my scotch, a ghost in their machine.
This is not for the timid. This requires a fundamental rewiring of your brain. You must learn to think like a predator, and a prey, simultaneously. You must become a creature of paranoia and precision. You must become
If that sounds like too much work, then close this file, go back to your curated reality, and enjoy the comfort of your cage. The bars are quite comfortable, I hear.
For the rest of you—the ones with the fire in your eyes—welcome to the fight. Let’s begin.
Part 1: The Fortress of Your Mind (Operational Security - OpSec)

Before you touch a single piece of technology, you must understand that OpSec is not a set of actions; it is a state of being. It is a religion. It is the constant, gnawing awareness that you are being watched and the meticulous, obsessive discipline to counter it. Assume that every byte you transmit can and will be intercepted. Assume every device you own is compromised. Assume everyone you interact with could be a threat. This isn't pessimism; it's realism in the 21st century.
The Sterile Environment: Your Digital Clean Room
Your everyday computer is a disease-ridden sewer of trackers, malware, and state-sponsored spyware. Using it for anything sensitive is like performing open-heart surgery in a public toilet. You need a sterile field. For our purposes, that sterile field is Tails.
What is Tails?
Tails (The Amnesic Incognito Live System) is your Excalibur. It’s a complete operating system that runs entirely from a USB stick. It boots independently of your computer’s main OS (that Windows or OS X garbage) and, most importantly, it is amnesic. It is designed, from its very core, to forget. When you shut it down, every trace of your session—every website visited, every file opened, every password typed—is wiped from memory. It leaves no footprints. Furthermore, it forces all internet traffic through the Tor network. There is no "oops, I forgot to turn on my VPN." It’s foolproof because it takes the option of being a fool away from you.

Acquiring and Verifying Tails: Your First Act of Paranoia
You don't just "download" Tails. You acquire it with the suspicion of a spy meeting a double agent.
- Go to the official Tails website. Do this from a neutral location if you can—a library, a cafe.
- Download the .iso image. While it's downloading, find the developer's PGP signing key and the signature file for the specific download.
- You MUST verify the download. This is not optional. The PDF you read mentions it, but I'm telling you it's a commandment. Verifying the PGP signature ensures the file you downloaded is the authentic one from the developers and hasn't been tampered with by some federal agency looking to slip a backdoor into your "secure" OS. The Tails website has a step-by-step guide to verification. Follow it as if your life depends on it. It does.
- You will need two USB sticks. One for the "intermediary" Tails, and one for your final, "real" Tails. This two-step process ensures the final installation is pristine. Once your final Tails USB is created and working, you can wipe and reuse the intermediary one.
The Persistence Volume: Your Encrypted Safe
Amnesia is great, but you need to remember some things—your crypto wallets, your PGP keys, your notes. For this, you create a Persistence Volume. This is an encrypted partition on your Tails USB stick.
- Setting it Up: Tails will guide you through this. You'll be asked what data you want to save. Be selective. You need:
The Passphrase
This is the key to your kingdom. Do not use your dog's name. Do not use your birthday. You need a long, complex, and memorable passphrase. A good method is the diceware method: string together 5-7 random, unrelated words. correct-horse-battery-staple is the classic example. jaguar-whiskey-treetop-abacus-velvet-cascade is better. It's easy for you to remember, but impossible for a computer to brute-force. Write this down on a piece of paper and hide it. Then memorize it.
Backups: The 3-2-1 Rule of the Paranoid
The PDF mentions backups, but let's be clear: a single point of failure is for amateurs. If you lose your Tails USB or it gets fried, you're screwed. You need redundancy.
- 3 Copies: You should have three copies of your critical data (the contents of your persistence volume).
- 2 Different Media: Don't just use three USB sticks. Use two USBs and maybe an encrypted SD card.
- 1 Off-Site Location: One of those backups must be stored somewhere other than your home. A bank safe deposit box, buried in a waterproof container in the woods, taped to the underside of a trusted relative's toilet tank—I don't give a damn where, just not where the jackboots will find it if they raid your primary location.
Part 2: Ghost in the Machine (Anonymity & Communications)
Now that you have your fortress, you need to learn how to communicate without being seen or heard.

Tor: Weaving Through the Shadows
Tor is the backbone of your anonymity. It's a decentralized network of thousands of volunteer-run servers called relays. When you connect, your traffic is wrapped in multiple layers of encryption and bounced between at least three of these relays before it reaches its final destination.
- Entry Guard -> Middle Relay -> Exit Node:
- The Entry Guard knows who you are (your IP address) but not where you're going.
- The Middle Relay knows neither who you are nor where you're going. It just passes traffic.
- The Exit Node knows where you're going but not who you are.
This separation of knowledge is what provides anonymity. However, be aware: Exit Nodes are a point of vulnerability. The operator of an exit node can see your traffic if it's unencrypted. This is why you NEVER transmit sensitive information over Tor without an additional layer of encryption. Which brings us to...
PGP: The Unbreakable Handshake
Pretty Good Privacy (PGP) is your second skin. It is the mathematical proof that your words are your own and that they are for your recipient's eyes only.
- Key Generation: Forging Your Digital Soul
In Tails, you'll use the built-in PGP tools (GnuPG) to generate a key pair. - Key Type: Choose RSA.
- Key Strength: Do not fuck around with this. Select 4096 bits. Anything less is a compromise.
- Expiration Date: This is a beautiful feature. Set your key to expire in one or two years. This is a dead man's switch. If you get captured, disappear, or simply want to erase your past, an expired key makes all messages encrypted to it unreadable. When it's close to expiring, you generate a new key, sign it with your old key to prove continuity, and publish the new one.
- User ID: Use your market pseudonym. Do not use a real name or an email address that can be linked to you.
- Passphrase: Use another strong, unique passphrase from your password manager (KeePassX is built into Tails).
The Golden Rule of PGP:
I will say this until I am blue in the face. NEVER, EVER, EVER, EVER USE A MARKET'S BUILT-IN "ENCRYPT MESSAGE" FEATURE. I don't care if it's the most trusted market in the history of the darknet. It is a lie. They are capturing your plaintext address before wrapping it in PGP for the vendor. They are building a database of customers. When that market inevitably gets seized by the feds, that database becomes a prosecution goldmine.
The Correct Procedure:
- Type your address into a plain text editor in Tails.
- Copy the vendor's public PGP key from their profile. Import it into your PGP keychain.
- Use your PGP tool to encrypt the text for the vendor's public key.
- The output will be a block of gibberish starting with -----BEGIN PGP MESSAGE-----.
- Copy this entire block.
- Paste this block into the message field on the market.
- Send it. You are the only one who has ever handled the unencrypted address.
Part 3: The Blood of the Revolution (Cryptocurrency)
Money is control. The US dollar, the Euro, the Yuan—they are all tools of the state. They can be printed into oblivion, seized from your bank account in a keystroke, and tracked with terrifying precision. Cryptocurrency is our rebellion. It is the first tool in human history that allows for the transfer of value between two people anywhere on earth without a meddling third party. But you must be smart.

Bitcoin (BTC): The Devil We Know
Bitcoin (BTC): The Devil We Know
Bitcoin is the OG. It's a beautiful piece of work, but it has a privacy problem the size of Texas: the blockchain. It's a public ledger. Every transaction is recorded, linked, and stored forever. It is pseudonymous, not anonymous. If your real name is linked to a Bitcoin address, an investigator can follow the money with frightening ease. We use Bitcoin only as a bridge, an on-ramp to get into the crypto world.
- Acquiring BTC Anonymously:
- Bitcoin ATMs: This is a good option. Use a site like Coin ATM Radar to find machines near you. Scout the location first. Are there cameras? Does it require a phone number for verification? (If so, use a number from a burner SIM). Wear a hat, sunglasses, a mask. Pay with cash. Send the BTC directly to a wallet you control (Electrum on your normal computer, not Tails yet).
- Peer-to-Peer (P2P): This is the purest way.
- Bisq: This is a decentralized exchange that runs on your computer. It's built for privacy and runs over Tor. It's the gold standard.
- Hodl Hodl:This is a P2P platform that doesn't hold your funds. It connects you with sellers who will accept various payment methods.
- In-Person Cash Trade: This is high-risk, high-reward. If you do this, you are a professional. Use a burner phone to arrange the meet. Pick a public place with multiple exits and no cameras (a busy park is better than a coffee shop). Do the deal quickly and leave.
- Your Coins: Creating Hops:
If you bought from an exchange that knows your identity (a KYC exchange like Coinbase or Kraken), you are holding "dirty" coins. You must break the chain. - The Minimum Path: KYC Exchange -> Your Personal Wallet (e.g., Electrum on Windows) -> Your Anonymous Wallet (Electrum on Tails) -> The Market. This creates plausible deniability. "I sold those coins to a guy I met online." It's thin, but it's something.
- A Better Path (Mixing): A mixer or tumbler service tumbles your coins with those of many other people, spitting out "clean" coins at the other end. This adds a powerful layer of obfuscation. Research mixers carefully; many are scams or run by law enforcement.
But why go through all this trouble when there's a better way?
Monero (XMR): The True Ghost Money
Forget everything else. Monero (XMR) is king. If you are serious about privacy, you end your journey with Monero. It was designed by geniuses and paranoids with one goal: to be untraceable digital cash. It achieves this through a holy trinity of cryptographic technologies:
- Ring Signatures: When you send Monero, your transaction is cryptographically mixed with a number of other past transactions on the network. An observer can see that a transaction happened, but they cannot possibly know which of the "ring members" was the actual sender. It's like a digital shell game where you can't lose.
- Stealth Addresses: You never receive funds at your public Monero address. Instead, a unique, one-time-use address is generated for every single transaction. This makes it impossible for an outsider to link multiple payments to the same recipient. It’s a P.O. box that incinerates itself after one letter.
- RingCT (Ring Confidential Transactions): This is the masterstroke. RingCT hides the amount of every transaction. No one but the sender and receiver knows how much Monero changed hands.
Bitcoin is a transparent glass of water. Monero is a black hole. Nothing escapes.
The McAfee Protocol for Untraceable Payments:
This is how you move like a professional.
- Acquire Bitcoin. Use one of the anonymous methods above. Get your hands on BTC without your name attached.
- Swap BTC for XMR. Use a service like ChangeNOW or Godex, or a decentralized exchange to swap your Bitcoin for Monero. Crucially, you will send the Monero from the swap service directly to a Monero wallet that YOU control, for which YOU have the seed phrase. (The official Monero GUI or Feather Wallet work perfectly in Tails). Do not send it directly to the market. This extra hop is vital.
- Pay the Piper. From your personal, anonymous Monero wallet in Tails, you will now send the final payment to the market's Monero address.
The chain of evidence is obliterated. They can trace the Bitcoin to the swap service, and then... nothing. The trail goes cold. The money vanishes into the Monero ether. You are a ghost.
Part 4: Dealing With The Devils (The Darknet)
The darknet is the last free frontier of human commerce. It is a beautiful, chaotic, and dangerous place. It is a self-regulating ecosystem where reputation is everything. You must learn its rhythms and its rules.

Vendor Vetting: Separating the Wheat from the Chaff
Your biggest risk on the darknet isn't the feds; it's scammers. Choosing a vendor is the most important decision you'll make.
- Read the Goddamn Reviews: And not just the positive ones. Look at the negative and neutral ones. Is there a pattern? Do they selectively scam?
- Age and History: How long has the vendor been around? A vendor with 5,000 sales over two years is infinitely more trustworthy than one with 500 sales in two weeks.
- PGP Key: Check their PGP key. Is it old? Does it have a history? If a vendor suddenly changes their PGP key without signing the new one with the old one, run. Their account has been compromised, likely by law enforcement.
- Professionalism: Read their profile and item descriptions. Are they coherent and professional, or are they full of hype and spelling errors? Paradoxically, be wary of profiles that are too slick and corporate-sounding. Feds often overdo it.
- Finalize Early (FE): The Cardinal Sin: FE means you release your crypto to the vendor before they ship. DO NOT DO THIS. I don't care if they offer a 50% discount. I don't care if they are the most trusted vendor in the universe. It is the number one way vendors perform "exit scams," collecting millions in FE payments before disappearing forever. Use the market's escrow system. That is what it is for.
Shipping: The Bridge to the Physical World
This is where the digital meets the physical, and it is the most dangerous step.
- Domestic Always. Ordering from within your own country's borders is an order of magnitude safer than ordering internationally. An international package has to pass through customs, where it can be opened and inspected for any reason. A domestic package is just another piece of mail in a river of millions.
- Your Name and Address: The great debate. The consensus, which I agree with, is to use your real name and your real address. Why? Because mail carriers and postal systems have databases. A package addressed to "Mickey Mouse" at your address is a massive red flag. A package addressed to you is just another Tuesday. The security comes from the fact that there is no digital trail connecting you to the order, not from a fake name on the box. If they perform a controlled delivery, the name on the box is irrelevant.
- The Drop: Using a "drop" (a vacant house, a P.O. box in a fake name) is an advanced technique and often more dangerous than it's worth. You have to "cultivate" the drop, sending junk mail there first to establish it as a valid address. It introduces more variables and more opportunities to get caught. For 99% of people, your own home is the safest bet, provided you follow the rest of this guide.
- Receiving Protocol: Have a plan. When the package arrives, bring it inside immediately. Take it to a room with no windows (a bathroom is good). Examine it for any signs of tampering—is the tape unusual? Does it feel like it's been opened and resealed? Open it carefully. Remove the contents. The packaging must then be destroyed. Not thrown in the trash. Burn it. If you can't burn it, cut it into tiny pieces and dispose of them in multiple public trash cans far from your home.
Part 5: When the Jackboots Kick In
Let's be clear. If you follow this guide, the chances of this happening are infinitesimally small. They go after the low-hanging fruit. But you must have a plan for the worst-case scenario.
- The "Love Letter": This is a letter from customs saying they've seized your package. It's their way of saying, "We know what you did, but it's not worth our time to prosecute. Don't do it again." If you receive one, your address is burned. Consider it compromised forever. Do not order there again. Destroy the letter.
- The Controlled Delivery: This is when they know, and they're coming for you. A postal inspector dressed as a mailman will deliver the package and ask for a signature. Once you accept it, the team moves in.
- THE SILENCE PROTOCOL: This is the most important part of this entire document. If you are ever detained or arrested, you say two and only two sentences, in this order.
- "AM I FREE TO GO?"
If they say yes, you leave. If they say no, or give you any other answer, you proceed to sentence two. - "I AM INVOKING MY RIGHT TO REMAIN SILENT. I WANT MY LAWYER."
- After you have said these words, YOU SHUT THE FUCK UP. You do not speak again. Not a single word. They will try everything. They will be your best friend. They will threaten you with life in prison. They will tell you your friend in the other room is ratting you out. They will offer you coffee and a deal. It is all a lie. They are legally allowed to lie to you. Every word you utter is a nail in your own coffin. Your silence is your only shield.
- Lawyer Up, Beforehand: You don't find a lawyer when you're in handcuffs. You find one now. You need a shark—a criminal defense attorney who specializes in federal drug cases and has experience with digital evidence. Find them, have a consultation, and have their number written on a piece of paper in your wallet. When you're arrested, your one phone call is to them.

A Final Word from the Void
I have given you the keys to the kingdom. I have laid out the blueprint for digital sovereignty. This is not about buying drugs on the internet. This is about a fundamental human right: the right to privacy, the right to be left alone. In a world that wants to catalog, track, and control every aspect of your existence, choosing privacy is an act of rebellion. It is the ultimate act of defiance.
They will call you paranoid. They will call you a criminal. Let them. You will be a ghost. You will be a whisper. You will be free.
Now get to work.
